As businesses continue to embrace digital transformation, cloud computing has become a fundamental part of modern IT infrastructure. Organizations now rely on cloud platforms to store data, run applications, and scale their operations more efficiently. While cloud technology offers flexibility, cost savings, and accessibility, it also introduces new security challenges. For this reason, understanding cloud security has become essential for companies operating in today’s digital landscape.

Cloud environments often host sensitive data, business applications, and critical services, which is why understanding common cloud security risks for business data is essential.Without proper security measures, these systems can become targets for cyberattacks, data breaches, and unauthorized access. Companies that invest in strong cloud security practices can protect their information, maintain compliance with regulations, and build trust with their customers. Technology leaders like SYNEXRA TECHNOLOGY SOLUTIONS CO., LTD. recognize that effective cloud security strategies are essential for helping businesses operate safely in an increasingly connected world. This article explores the key concepts of cloud security that every organization should understand.
What Is Cloud Security?
Defining Cloud Security
Cloud security refers to the technologies, policies, procedures, and controls designed to protect cloud-based systems, data, and infrastructure from cyber threats. It includes measures that safeguard information stored in cloud environments while ensuring authorized users can access resources when needed.
Cloud security covers several aspects of protection, including:
- Data security
- Application security
- Network security
- Identity and access management
- Infrastructure protection
Together, these components help organizations secure their cloud environments against potential vulnerabilities and attacks.
Why Cloud Security Matters for Businesses
Cloud services allow businesses to store large amounts of data and run critical applications remotely. However, this accessibility also creates potential risks if security measures are not properly implemented.
Strong cloud security helps businesses:
- Protect sensitive business data
- Prevent unauthorized access
- Reduce cybersecurity risks
- Maintain regulatory compliance
- Ensure operational continuity
By implementing effective security strategies, organizations can fully benefit from cloud computing while minimizing risks.
The Shared Responsibility Model
Understanding Shared Responsibilities
One of the most important concepts in cloud security is the shared responsibility model. This model defines the security responsibilities of both the cloud provider and the customer.
In most cloud environments:
- Cloud providers are responsible for securing the underlying infrastructure, including hardware, physical data centers, and core networking components.
- Customers are responsible for protecting their data, managing user access, and configuring cloud services securely.
Understanding this model is critical because many cloud security incidents occur when organizations assume that providers handle all security aspects.
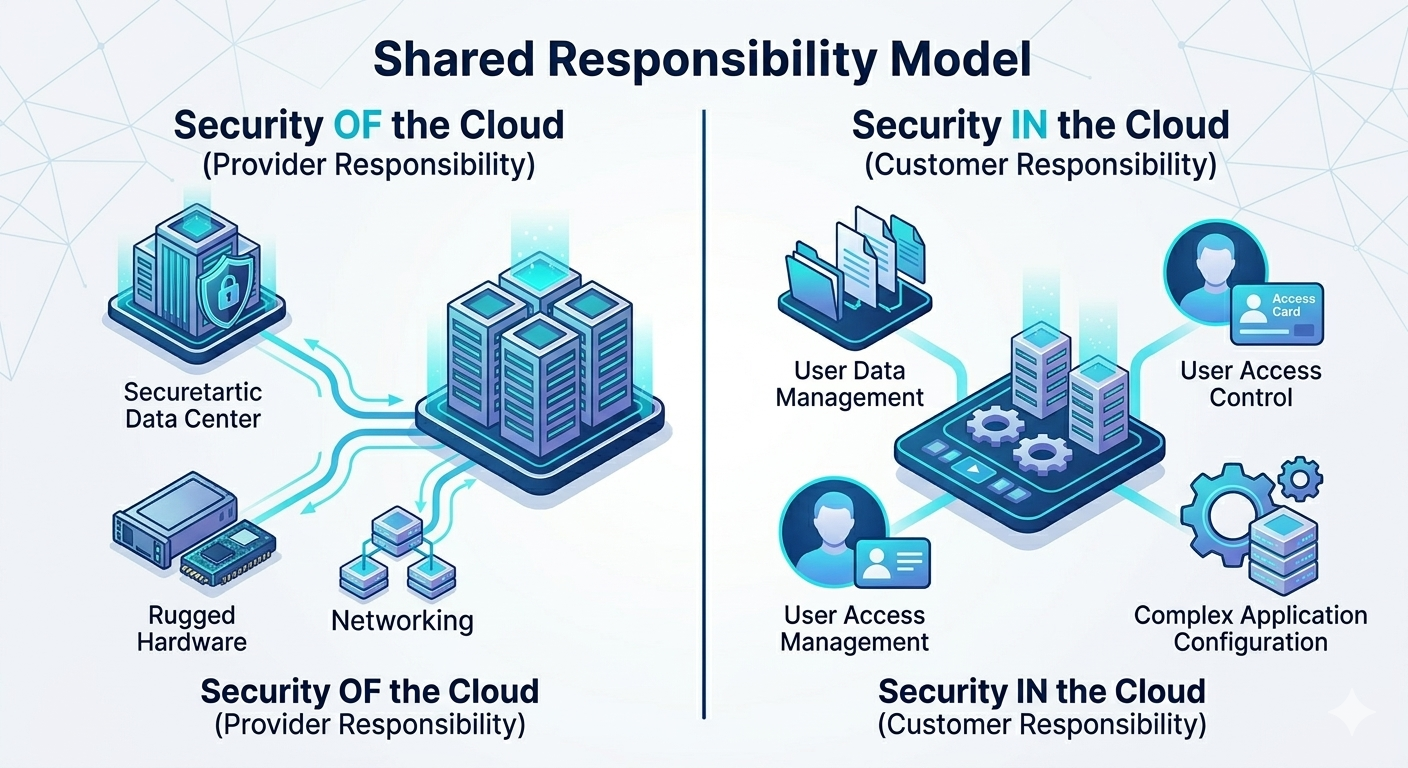
Security Responsibilities in Different Cloud Services
The level of responsibility varies depending on the type of cloud service used.
Common cloud service models include:
- Infrastructure as a Service (IaaS) – customers manage operating systems, applications, and data security.
- Platform as a Service (PaaS) – providers manage infrastructure while customers focus on application and data protection.
- Software as a Service (SaaS) – providers manage most infrastructure, but customers remain responsible for user access and data security.
Each model requires different security considerations.
Key Components of Cloud Security
Identity and Access Management (IAM)
Identity and Access Management systems control who can access cloud resources and what actions they are allowed to perform.
IAM solutions allow organizations to:
- Authenticate users
- Assign access permissions
- Monitor login activities
- Enforce security policies
Using role-based access control ensures that employees only have access to the resources necessary for their job functions.
Data Encryption
Encryption is one of the most effective ways to protect sensitive data in cloud environments. It converts readable data into encrypted formats that can only be accessed with proper keys.
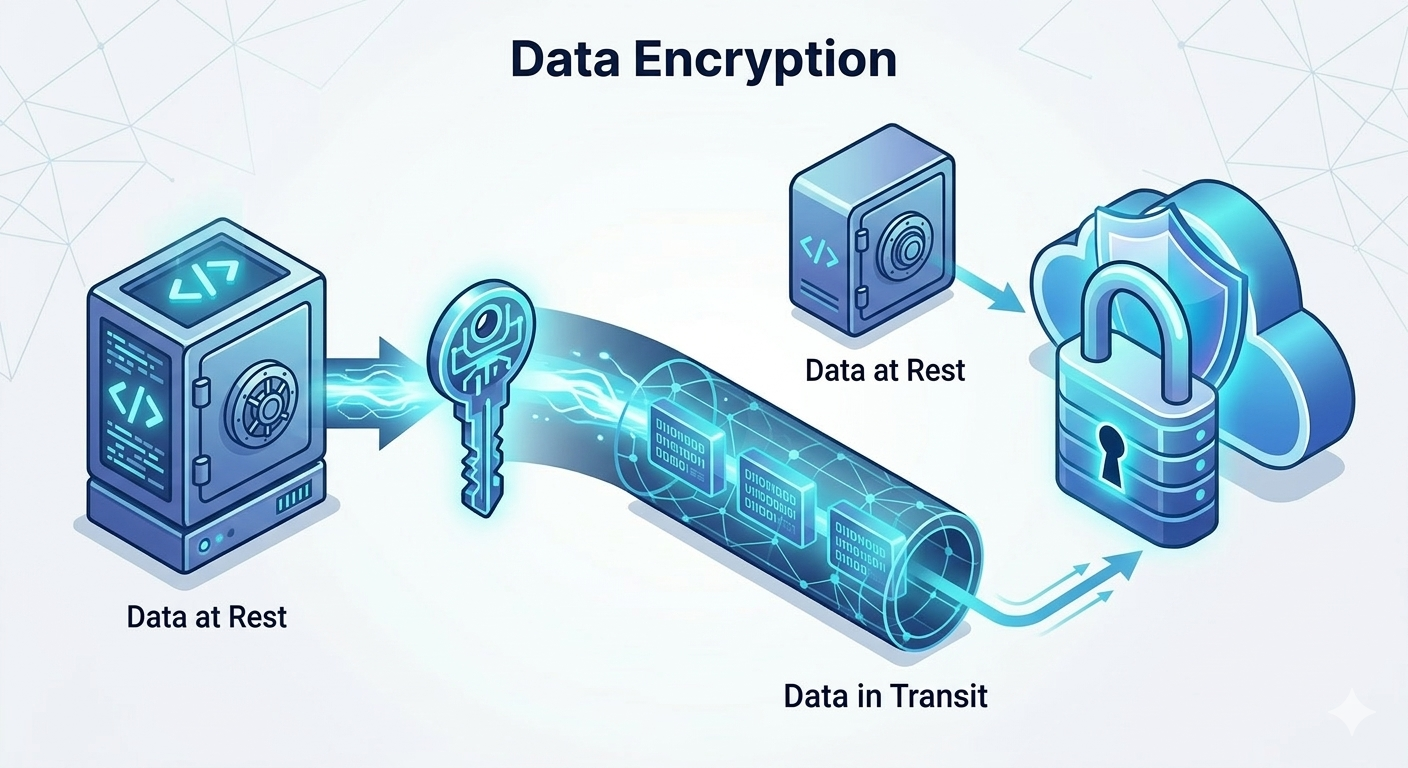
Two important types of encryption include:
- Encryption at rest – protects stored data within cloud databases and storage systems
- Encryption in transit – protects data while it is transmitted between users and cloud services
Encryption ensures that even if unauthorized individuals gain access to data, they cannot read or use it.
Network Security
Cloud network security focuses on protecting communication between cloud resources and users.
Key network security measures include:
- Virtual private networks (VPNs)
- Firewalls
- Network segmentation
- Intrusion detection systems
These tools help prevent unauthorized network access and protect cloud infrastructure from cyberattacks.
Common Cloud Security Threats
Data Breaches
Data breaches occur when unauthorized individuals gain access to sensitive information stored in the cloud. This can result from weak authentication systems, misconfigured storage settings, or compromised credentials.
A single breach can expose confidential business information, customer records, and financial data.
Misconfigured Cloud Settings
Cloud services provide many configuration options, but incorrect settings can lead to significant vulnerabilities.
Examples of misconfigurations include:
- Publicly accessible storage buckets
- Open databases without authentication
- Improper firewall rules
- Unrestricted administrative privileges
Regular configuration reviews and automated monitoring tools help organizations prevent these risks.
Insider Threats
Employees or contractors with legitimate access to cloud systems can pose security risks if they misuse their privileges.
Insider threats may include:
- Unauthorized data downloads
- Sharing credentials
- Accidental data exposure
- Deliberate data theft
Organizations should monitor user activity and implement strict access control policies.
Account Hijacking
Account hijacking occurs when attackers gain control of cloud accounts through phishing attacks, weak passwords, or credential theft.
Once attackers access an account, they may:
- Steal sensitive data
- Modify system settings
- Deploy malicious software
- Disrupt business operations
Multi-factor authentication helps significantly reduce this risk.
Best Practices for Cloud Security
Implement Strong Authentication
Authentication methods should ensure that only authorized users can access cloud resources.
Recommended security practices include:
- Multi-factor authentication (MFA)
- Strong password policies
- Biometric authentication
- Single sign-on solutions
These measures help prevent unauthorized access to cloud systems.
Use Continuous Monitoring
Monitoring tools provide real-time visibility into cloud environments. These tools track system activities and detect unusual behaviors.

Monitoring systems can identify:
- Suspicious login attempts
- Abnormal data transfers
- Unauthorized configuration changes
- Potential security breaches
Early detection allows security teams to respond quickly to threats.
Regular Security Audits
Security audits help identify vulnerabilities before they are exploited by attackers.
Regular assessments should include:
- Vulnerability scans
- Penetration testing
- Configuration reviews
- Compliance checks
These evaluations ensure that security controls remain effective.
Backup and Disaster Recovery
Even with strong security controls, unexpected events can still occur. Businesses should implement backup and disaster recovery plans to ensure data can be restored quickly by following a disaster recovery plan for business continuity.
Reliable backup strategies protect organizations from:
- Data corruption
- System failures
- Ransomware attacks
- Accidental data deletion
Regular backup testing ensures recovery systems function properly.
Compliance and Cloud Security
Meeting Regulatory Requirements
Many industries must comply with data protection regulations that require secure data storage and access management.
Compliance requirements may include:
- Encryption standards
- Access control policies
- Security monitoring systems
- Data retention rules
Organizations must ensure their cloud environments meet these legal requirements.
Protecting Customer Privacy
Customers trust businesses with their personal information. Strong cloud security measures demonstrate a commitment to protecting that data.
Organizations that prioritize security build stronger relationships with customers and enhance their reputation.
Emerging Trends in Cloud Security
Zero Trust Security
Zero Trust is a modern security model that assumes no user or device should be trusted by default. Every access request must be verified before granting permissions.
This approach reduces the risk of unauthorized access and internal threats.
Artificial Intelligence in Security
Artificial intelligence is increasingly used to enhance cloud security systems. AI tools can analyze large volumes of data to detect suspicious activities and potential threats.
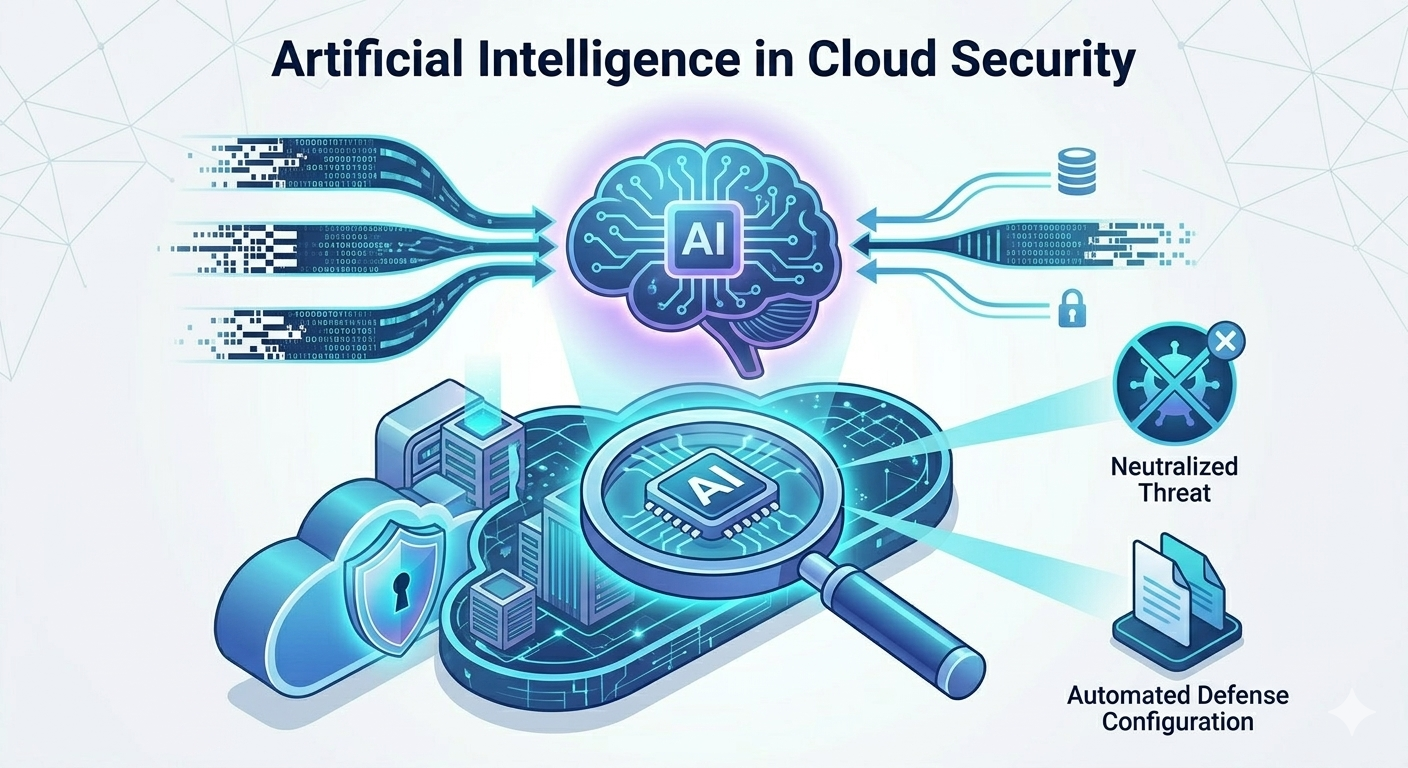
AI-driven security systems can:
- Identify anomalies
- Predict cyberattacks
- Automate threat responses
- Improve security monitoring
These technologies help organizations strengthen their cybersecurity defenses.
Automation and Security Orchestration
Automation tools help organizations manage cloud security more efficiently. Automated systems can detect vulnerabilities, enforce security policies, and respond to incidents without human intervention.
Security orchestration platforms integrate multiple security tools to create coordinated defense strategies.
Building a Strong Cloud Security Strategy
Developing a comprehensive cloud security strategy requires a combination of technology, policies, and employee awareness.
Organizations should focus on:
- Defining clear security policies
- Training employees on cybersecurity best practices
- Implementing advanced monitoring systems
- Conducting regular risk assessments
- Collaborating with trusted technology partners
These steps help businesses create secure cloud environments that support long-term growth.
Conclusion
Cloud computing has revolutionized how businesses manage data and deliver digital services. However, with these advancements come new security challenges that organizations must address. Understanding the key principles of cloud security allows companies to protect their systems, safeguard sensitive information, and maintain operational stability.
By implementing strong authentication systems, encryption technologies, monitoring tools, and compliance frameworks, businesses can significantly reduce their exposure to cyber threats. Cloud security should be viewed not as a one-time project but as an ongoing process that evolves alongside technological developments.
Forward-thinking organizations such as SYNEXRA TECHNOLOGY SOLUTIONS CO., LTD. understand that building secure cloud infrastructures is essential for modern digital operations. With the right security strategies and continuous improvement, businesses can confidently harness the power of cloud computing while protecting their most valuable digital assets.