As businesses continue to adopt cloud computing, organizations are increasingly relying on cloud infrastructure to store, manage, and process critical data. Cloud platforms offer scalability, flexibility, and cost efficiency that traditional IT systems cannot easily match. However, while the cloud provides many advantages, it also introduces new challenges related to data protection and cybersecurity. Understanding cloud security risks is essential for businesses that want to safeguard their digital assets and implement modern cloud security strategies for businesses.
Many companies assume that cloud providers are fully responsible for protecting their data. In reality, cloud security follows a shared responsibility model, where both the provider and the organization must implement proper security controls. Without a clear security strategy, sensitive information can be exposed to cyberattacks, misconfigurations, or unauthorized access.
Organizations such as SYNEXRA TECHNOLOGY SOLUTIONS CO., LTD. recognize that identifying and mitigating cloud security risks is a critical step in building secure and resilient cloud infrastructures. This article explores the most common data security risks in cloud environments and provides practical strategies for protecting business data.
Understanding Cloud Security Risks
What Are Cloud Security Risks?
Cloud security risks refer to vulnerabilities or threats that can compromise data stored or processed in cloud environments. These risks may arise from technical misconfigurations, insufficient security policies, malicious cyberattacks, or weak access controls.
Unlike traditional on-premise infrastructure, cloud systems are accessible through the internet and often distributed across multiple geographic locations. While this improves accessibility and scalability, it also increases the potential attack surface for cybercriminals.
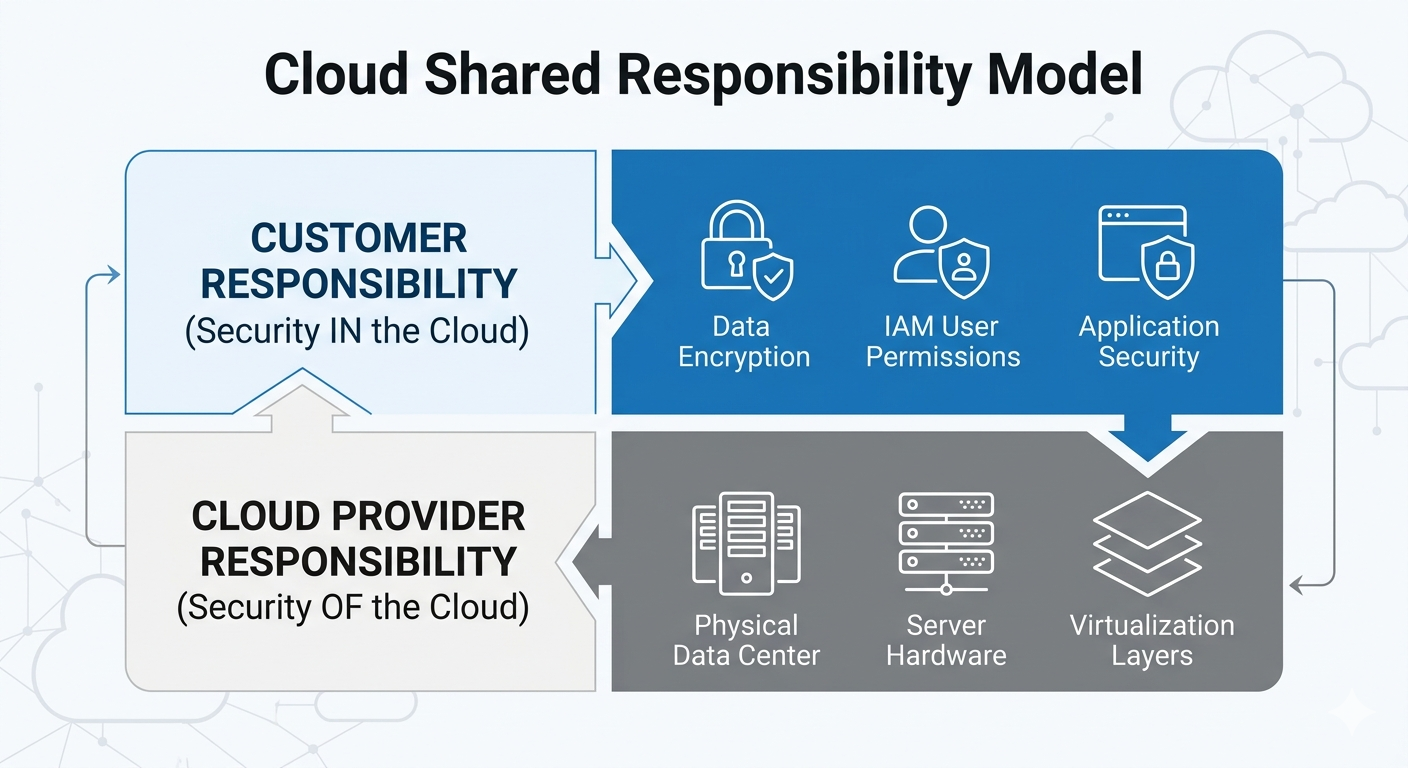
The Shared Responsibility Model
One of the most misunderstood aspects of cloud security is the shared responsibility model.
 ikeadecom
ikeadecom
Under this model:
- Cloud providers are responsible for securing the infrastructure, hardware, and underlying services.
- Customers are responsible for securing their data, applications, and user access.
If organizations fail to configure security settings correctly, sensitive data may become publicly accessible even if the cloud provider maintains secure infrastructure.
Understanding this responsibility split is crucial to managing cloud security risks effectively.
Major Cloud Security Risks Businesses Should Know
Data Breaches
Data breaches are among the most serious cloud security risks facing modern organizations. A data breach occurs when unauthorized individuals gain access to sensitive information stored in the cloud.

Common causes of cloud data breaches include:
- Weak authentication systems
- Misconfigured storage services
- Insecure APIs
- Compromised user credentials
The consequences of a breach can be severe, including financial losses, legal penalties, and reputational damage. Organizations must implement strong security controls to prevent unauthorized access to sensitive data.
Misconfigured Cloud Settings
Misconfiguration is one of the leading causes of cloud data exposure. Cloud platforms offer flexible configurations, but improper settings can accidentally expose sensitive information to the public internet.

Examples of misconfigurations include:
- Publicly accessible storage buckets
- Open databases without authentication
- Incorrect network firewall rules
- Unrestricted administrative privileges
Because cloud systems can be deployed quickly, security settings are sometimes overlooked during implementation. Continuous monitoring and configuration management are necessary to minimize these risks.
Insecure APIs and Interfaces
Cloud services rely heavily on APIs (Application Programming Interfaces) to allow applications to communicate with cloud resources. However, poorly secured APIs can create vulnerabilities that attackers exploit.
API-related risks include:
- Weak authentication mechanisms
- Insufficient input validation
- Lack of encryption
- Improper access controls
Cybercriminals often target APIs because they act as gateways to critical systems and databases. Securing APIs through authentication, encryption, and monitoring is essential to protecting cloud environments.
Unauthorized Access and Account Hijacking
Unauthorized access occurs when attackers gain control of cloud accounts through stolen credentials, phishing attacks, or brute-force password attempts.
Account hijacking allows attackers to:
- Access sensitive business data
- Modify system configurations
- Deploy malicious workloads
- Disrupt services
Implementing strong authentication mechanisms such as multi-factor authentication (MFA) can significantly reduce the risk of unauthorized account access.
Insider Threats
Insider threats are another important cloud security risk. Employees or contractors with legitimate access to cloud systems may intentionally or accidentally compromise sensitive data.
Examples include:
- Downloading confidential information without authorization
- Sharing credentials with unauthorized individuals
- Accidentally deleting critical data
- Misusing administrative privileges
Organizations must implement strict access policies and monitoring systems to detect suspicious behavior within cloud environments.
Data Loss in Cloud Environments
Accidental Deletion
Human error remains a major cause of data loss in cloud systems. Employees may accidentally delete files, overwrite important data, or misconfigure storage systems.
Without proper backup strategies, such mistakes can result in permanent data loss.
Automated backup systems and version control mechanisms help prevent these issues.
Ransomware Attacks
Ransomware attacks can also affect cloud storage systems. In these attacks, cybercriminals encrypt data and demand payment for its release.
If cloud data is not properly backed up or protected, organizations may face significant operational disruptions.
Implementing strong endpoint security and backup strategies can reduce the impact of ransomware threats.
Lack of Visibility and Monitoring
Limited Security Visibility
Many organizations struggle with limited visibility into cloud environments. Because cloud resources are distributed and dynamically created, it can be difficult to track all assets and security activities.
Without proper monitoring tools, security teams may not detect suspicious activities until significant damage occurs.
Cloud security monitoring solutions help organizations maintain real-time visibility into system activities and detect potential threats.
Shadow IT
Shadow IT refers to the use of unauthorized cloud services or applications by employees without the approval of the IT department.
These unauthorized tools may lack proper security configurations, increasing the risk of data leaks or cyberattacks.
Organizations must implement policies and monitoring tools to identify and control shadow IT activities.
Compliance and Regulatory Risks
Many industries must comply with strict data protection regulations. Storing sensitive data in cloud environments without proper security measures can lead to compliance violations.
Examples of compliance concerns include:
- Improper data storage locations
- Lack of encryption for sensitive data
- Inadequate access controls
- Insufficient audit logs
Non-compliance can result in heavy fines, legal action, and loss of customer trust. Implementing strong security frameworks helps organizations meet regulatory requirements.
Best Practices to Reduce Cloud Security Risks
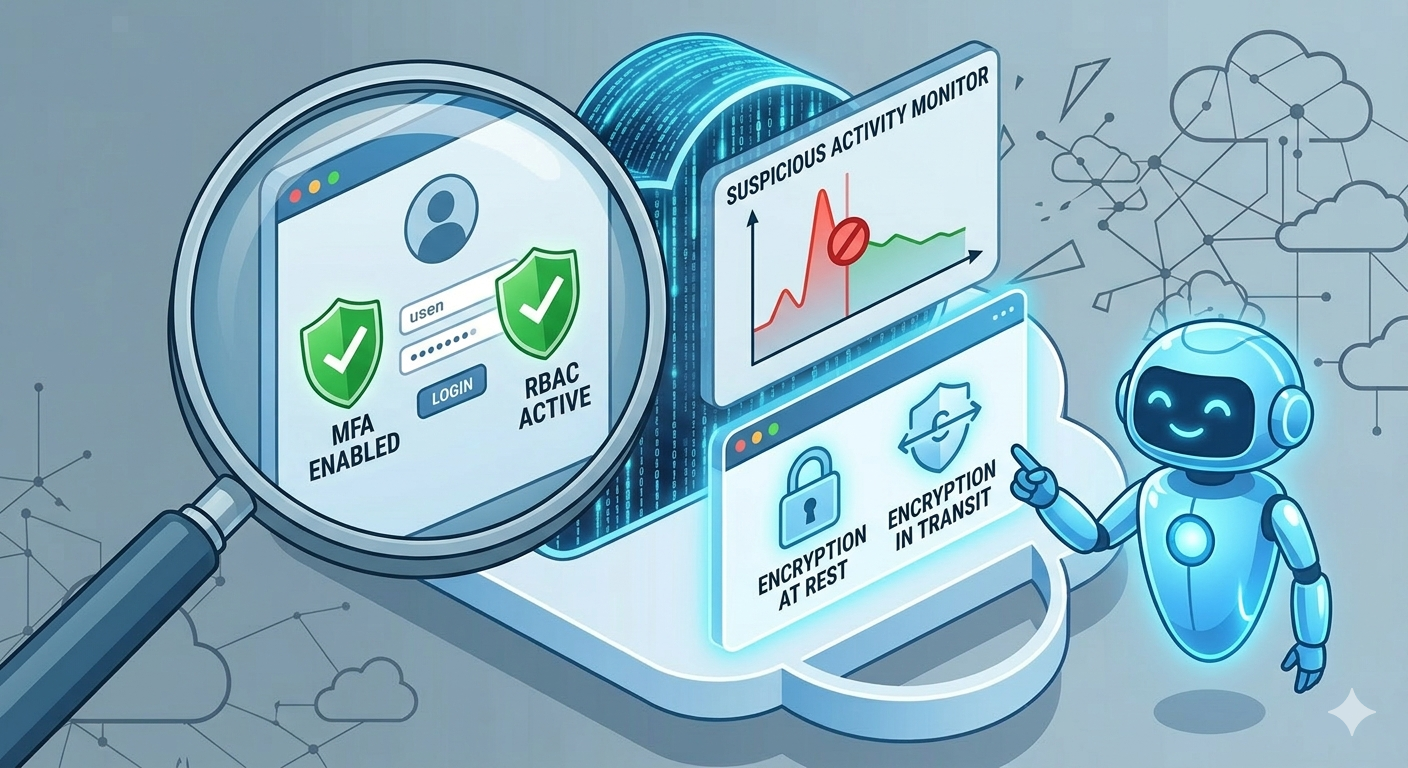
Implement Strong Access Controls
Access management is one of the most important defenses against cloud security risks.
Best practices include:
- Role-based access control (RBAC)
- Multi-factor authentication (MFA)
- Identity and access management (IAM) systems
- Regular review of user permissions
Limiting access to only necessary resources significantly reduces potential security threats.
Encrypt Data in Transit and at Rest
Encryption protects sensitive data from unauthorized access. Organizations should ensure that data is encrypted both while being transmitted and when stored in cloud systems.
Encryption helps prevent attackers from reading sensitive data even if they gain access to storage systems.
Use Continuous Security Monitoring
Security monitoring tools allow organizations to detect suspicious activities in real time.
These tools can monitor:
- Login attempts
- Network traffic
- Data access patterns
- System configuration changes
Automated alerts enable security teams to respond quickly to potential threats.
Conduct Regular Security Audits
Security audits help organizations identify vulnerabilities before attackers exploit them.
Regular assessments should include:
- Vulnerability scanning
- Penetration testing
- Configuration reviews
- Compliance checks
Continuous security evaluation ensures that cloud systems remain protected as technologies evolve.
Maintain Reliable Backup and Recovery Systems
Backup strategies are essential for protecting against data loss and ransomware attacks.
Effective backup plans include:
- Automated backup schedules
- Offsite data storage
- Backup encryption
- Disaster recovery testing
Reliable backup systems ensure that organizations can recover quickly from unexpected incidents, highlighting the importance of a disaster recovery plan for every company.
The Role of Advanced Technologies in Cloud Security
Artificial Intelligence in Threat Detection
Artificial intelligence is increasingly used to detect and respond to cybersecurity threats in cloud environments. AI systems can analyze massive amounts of data and identify suspicious patterns that human analysts might miss.
This allows organizations to detect attacks earlier and respond faster.
Zero Trust Security Models
Zero Trust security models assume that no user or system should be trusted by default. Every access request must be verified before being granted.
Key principles of Zero Trust include:
- Continuous authentication
- Strict access controls
- Micro-segmentation of networks
- Continuous monitoring
This approach significantly reduces the impact of potential security breaches.
Building a Strong Cloud Security Strategy
To effectively manage cloud security risks, organizations must adopt a comprehensive security strategy that combines technology, policies, and employee awareness.
A strong strategy includes:
- Clear cloud security policies
- Security training for employees
- Automated security monitoring
- Continuous risk assessments
- Collaboration between IT and security teams
By integrating these elements, businesses can build secure and resilient cloud infrastructures.
Conclusion
Cloud computing has transformed the way businesses store and manage data, but it also introduces new cybersecurity challenges. Understanding and mitigating cloud security risks is essential for protecting sensitive information, maintaining compliance, and ensuring operational stability.

Organizations must implement comprehensive security measures including access control, encryption, monitoring, and regular security assessments. By adopting best practices and leveraging advanced security technologies, companies can significantly reduce their exposure to cloud-based threats.
Forward-thinking organizations such as SYNEXRA TECHNOLOGY SOLUTIONS CO., LTD. recognize that proactive cloud security strategies are essential for successful digital transformation. With the right approach to risk management and data protection, businesses can confidently leverage cloud technologies while maintaining strong security and trust in the digital era.