In the modern digital economy, data has become one of the most valuable assets a company possesses. From customer information and financial records to intellectual property and operational analytics, organizations depend heavily on digital data to run their daily operations and drive growth. However, as technology advances and businesses become more interconnected, the risks associated with cyber threats, data breaches, and unauthorized access have also increased significantly. For this reason, data protection has become a top priority for organizations of all sizes.
Businesses must implement effective strategies to protect sensitive information and maintain the trust of customers, partners, and stakeholders. Without strong security measures, companies risk financial losses, legal consequences, and severe reputational damage. Forward-thinking organizations such as SYNEXRA TECHNOLOGY SOLUTIONS CO., LTD. understand that protecting business data requires a proactive approach that combines technology, policy, and employee awareness. This article explores the fundamental strategies companies can adopt to ensure strong data protection in today’s digital age.
Understanding Data Protection in the Digital Era
What Is Data Protection?
Data protection refers to the practices, policies, and technologies used to safeguard sensitive information from loss, corruption, unauthorized access, or cyberattacks, which is a core part of database security for modern businesses. It involves ensuring that data remains secure while still being accessible to authorized users when needed.

The primary goals of data protection include:
- Confidentiality – ensuring only authorized users can access data
- Integrity – maintaining the accuracy and reliability of information
- Availability – ensuring data remains accessible for business operations
These three principles form the foundation of modern cybersecurity frameworks and data protection strategies.
Why Data Protection Is Important for Businesses
Data protection is critical because businesses rely on data for nearly every aspect of their operations. If sensitive information is compromised, organizations may experience severe disruptions.
Key reasons why data protection is essential include:
- Protecting customer privacy
- Preventing financial losses
- Ensuring regulatory compliance
- Maintaining brand reputation
- Supporting business continuity
As cyber threats continue to evolve, organizations must continuously improve their data protection strategies to stay ahead of potential risks.
Common Data Threats Facing Modern Businesses
Cyberattacks and Data Breaches
Cyberattacks are among the most significant threats to business data. Hackers often target companies to gain access to valuable information such as financial records, personal identities, or trade secrets.
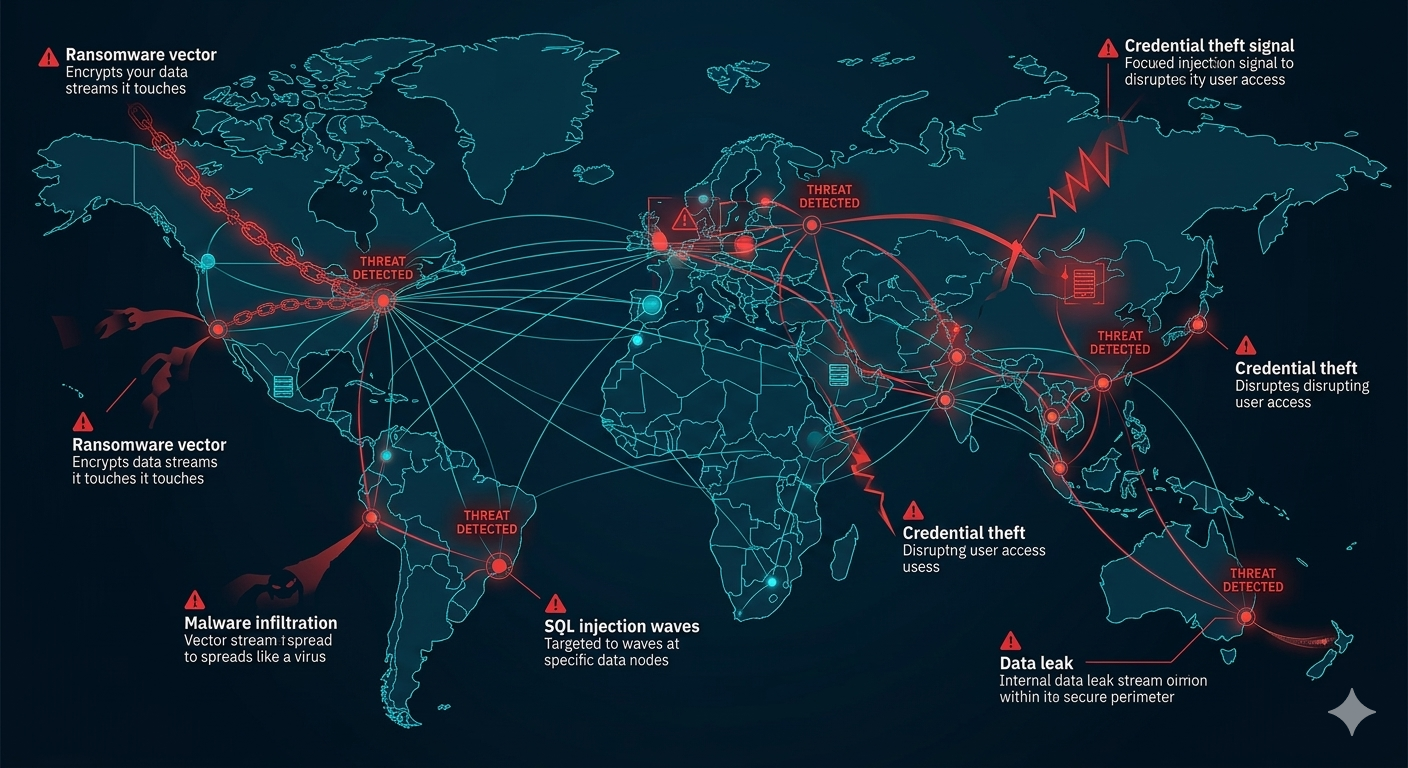
Common attack methods include:
- Phishing attacks
- Malware infections
- Ransomware attacks
- SQL injection
- Credential theft
A successful data breach can expose thousands or even millions of sensitive records, causing long-term damage to an organization.
Insider Threats
Not all data security risks come from external hackers. Insider threats occur when employees, contractors, or partners misuse their access to sensitive information.
Insider threats may involve:
- Unauthorized data access
- Accidental data leaks
- Intentional data theft
- Mishandling confidential files
Implementing strict access controls and monitoring systems helps organizations detect and prevent insider-related risks.
Human Error
Human error is one of the most common causes of data loss. Employees may accidentally delete files, send sensitive information to the wrong recipient, or fail to follow proper security protocols.
Even simple mistakes can lead to serious data exposure. This is why employee training plays a crucial role in effective data protection.
Core Strategies for Effective Data Protection
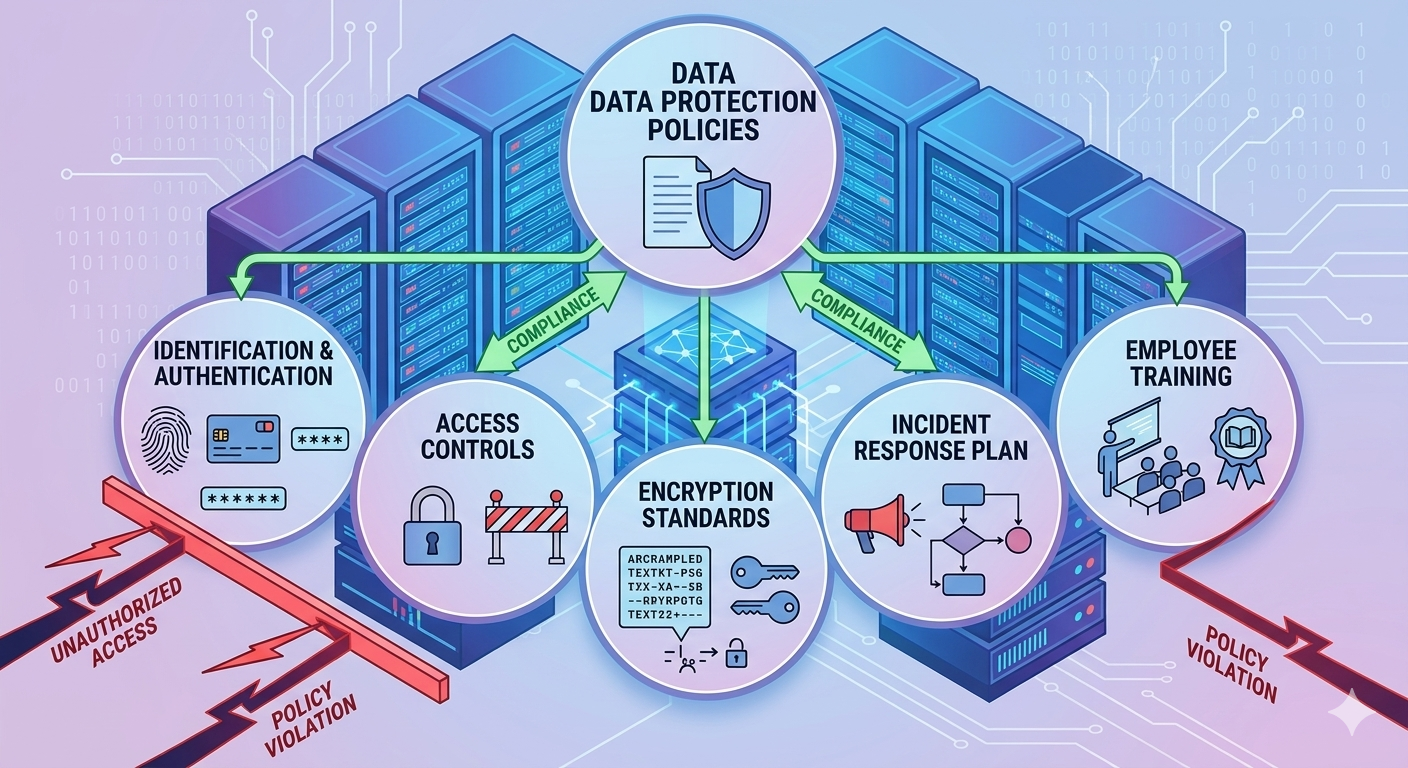
Implement Strong Access Controls
One of the most effective ways to protect business data is to limit access to sensitive information.
Access control mechanisms ensure that only authorized individuals can view or modify specific data. Businesses can implement:
- Role-based access control (RBAC)
- Identity and access management systems
- Multi-factor authentication (MFA)
- The principle of least privilege
By limiting access to only those who truly need it, organizations significantly reduce the risk of data breaches.
Encrypt Sensitive Data
Encryption is a critical component of modern data protection. It transforms readable information into an encoded format that can only be accessed with the proper decryption key.
There are two main types of encryption used by businesses:
- Encryption at rest – protects stored data in databases or storage systems
- Encryption in transit – protects data while it is transferred across networks
Encryption ensures that even if attackers gain access to stored data, they cannot easily read or use it.

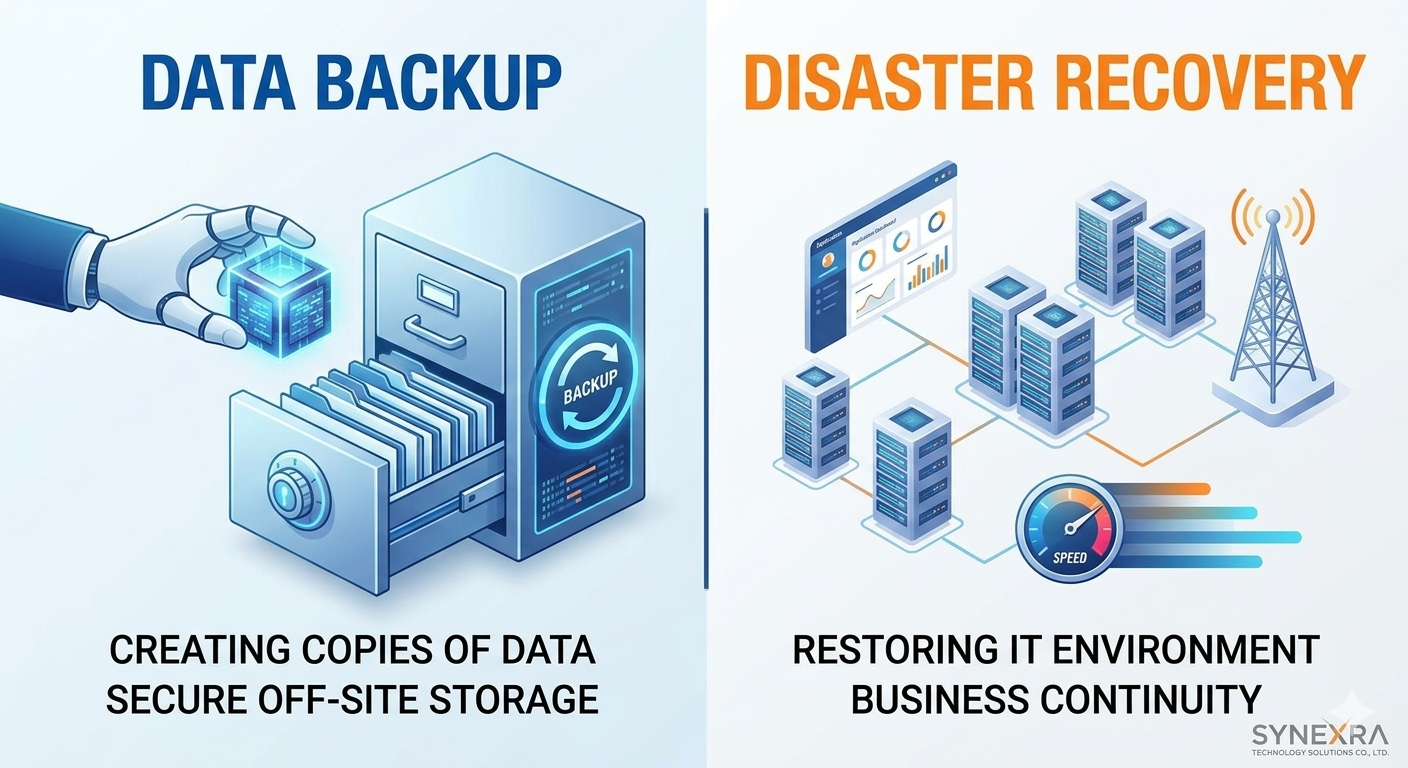
Regular Data Backups
Data backups are essential for protecting businesses from data loss caused by cyberattacks, hardware failures, or accidental deletions, which is why companies should implement a disaster recovery plan for business continuity.
An effective backup strategy should include:
- Automated backup schedules
- Offsite or cloud-based backups
- Backup encryption
- Regular backup testing
Backups ensure that critical business data can be restored quickly in case of emergencies.
Strengthening Organizational Data Protection Policies
Establish Clear Data Security Policies
Organizations should develop formal data protection policies that define how information is stored, accessed, and shared.
These policies should cover:
- Data classification standards
- User access procedures
- Data storage guidelines
- Incident response plans
- Data retention policies
Clear policies help ensure that employees understand their responsibilities when handling sensitive information.
Provide Employee Security Training
Employees are often the first line of defense against cyber threats. Providing regular cybersecurity training helps staff recognize and avoid common security risks.
Training programs should include:
- Phishing awareness
- Secure password practices
- Safe data handling procedures
- Reporting suspicious activities
Educated employees are far less likely to fall victim to cyberattacks.
Monitor and Audit Data Access
Continuous monitoring is essential for detecting suspicious activities related to data access.
Monitoring systems can track:
- Login attempts
- File access patterns
- Unusual data transfers
- Privilege changes
Audit logs allow security teams to investigate incidents and ensure compliance with internal policies.
Leveraging Modern Technologies for Data Protection
Cloud Security Solutions
Many businesses now rely on cloud platforms to store and process data. While cloud computing offers numerous advantages, it also introduces unique security challenges.
Organizations must ensure that cloud environments are configured securely by implementing:
- Identity and access management
- Cloud encryption services
- Security monitoring tools
- Data loss prevention systems
Proper cloud security measures help protect data stored in distributed environments.
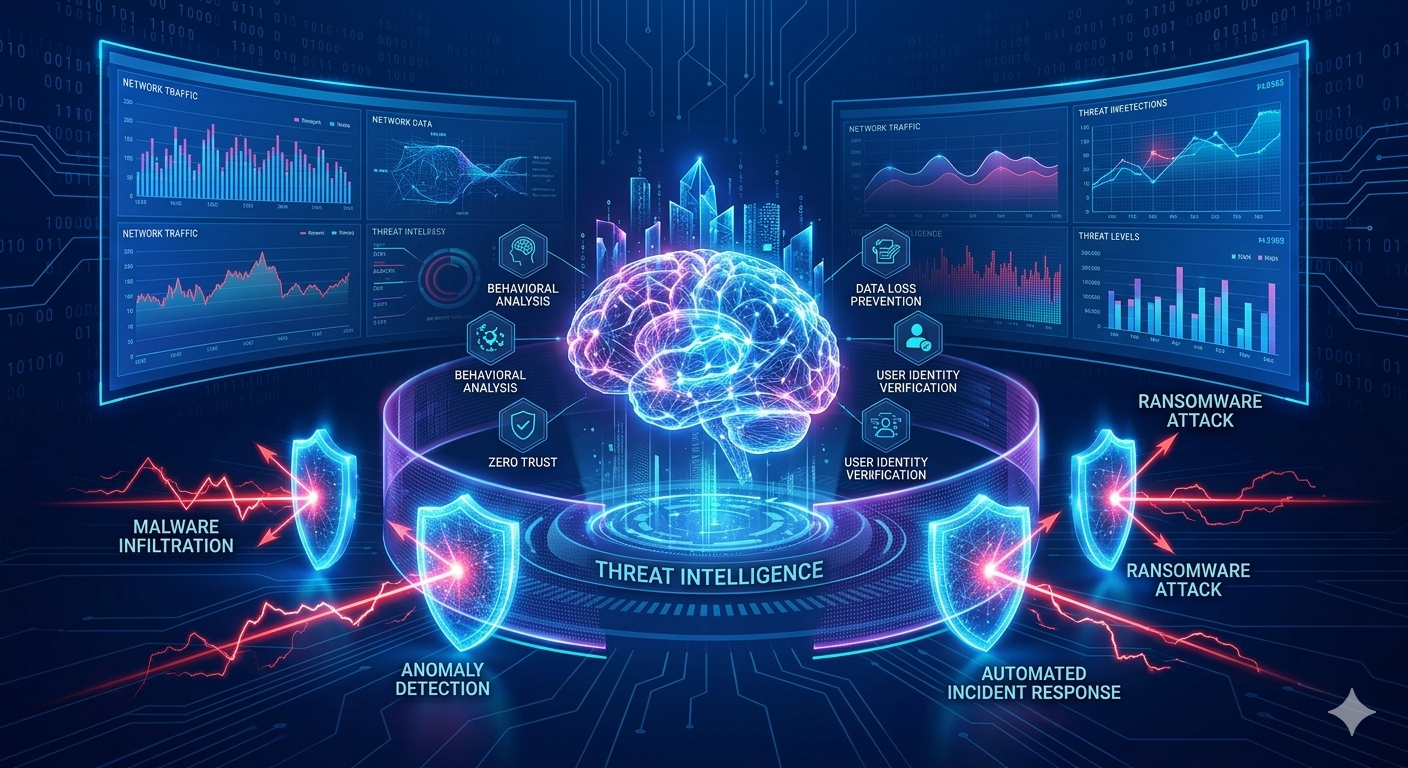
Artificial Intelligence in Cybersecurity
Artificial intelligence is becoming an important tool in modern data protection strategies. AI-powered security systems can analyze large volumes of data and identify suspicious patterns that may indicate cyber threats.
AI technologies can help with:
- Threat detection
- Behavioral analysis
- Automated incident response
- Fraud detection
These advanced systems enable organizations to detect and respond to threats more quickly.
Data Loss Prevention (DLP) Technologies
Data Loss Prevention tools help organizations monitor and control the movement of sensitive information across networks and devices.
DLP systems can:
- Identify confidential data
- Block unauthorized data transfers
- Monitor file sharing activities
- Prevent accidental data leaks
Implementing DLP solutions strengthens overall data protection efforts.
Regulatory Compliance and Data Protection
Meeting Legal Requirements
Many industries must comply with strict data protection regulations that govern how personal and financial data is handled.
Regulatory frameworks often require organizations to implement:
- Strong encryption methods
- Data access controls
- Security monitoring systems
- Incident reporting procedures
Compliance helps protect consumers while also ensuring that businesses maintain responsible data management practices.
Building Customer Trust
Customers expect businesses to protect their personal information. Strong data protection practices demonstrate that an organization takes privacy seriously.
When companies prioritize data security, they gain:
- Greater customer confidence
- Stronger brand reputation
- Increased competitive advantage
Trust has become one of the most valuable assets in the digital economy.
Future Trends in Data Protection
As technology continues to evolve, data protection strategies must adapt to new threats and innovations.
Emerging trends include:
- Zero Trust security architectures
- AI-driven threat detection
- Automated security monitoring
- Advanced encryption technologies
- Privacy-enhancing computing
Organizations that stay ahead of these trends will be better equipped to protect their digital assets.
Building a Culture of Data Security
Data protection is not just a technological challenge—it is also a cultural one. Every employee within an organization must understand the importance of protecting sensitive information.
Companies should foster a security-focused culture by:
- Promoting security awareness
- Encouraging responsible data handling
- Rewarding compliance with security policies
- Maintaining transparent communication about cybersecurity risks
When security becomes part of everyday business practices, organizations become significantly more resilient against cyber threats.
Conclusion
In the digital age, protecting business data is essential for maintaining operational stability, customer trust, and long-term growth. Cyber threats, insider risks, and human errors continue to challenge organizations worldwide, making strong data protection strategies more important than ever.
Businesses must implement comprehensive security measures that include encryption, access control, monitoring systems, employee training, and reliable backup solutions. By combining advanced technologies with well-defined policies and security awareness, organizations can significantly reduce the risk of data breaches and information loss.
Innovative companies such as SYNEXRA TECHNOLOGY SOLUTIONS CO., LTD. recognize that effective data protection is a fundamental component of modern digital infrastructure. By adopting proactive security strategies and continuously improving their defenses, businesses can safeguard their most valuable asset—data—while confidently navigating the challenges of the digital era.