In today’s digital economy, data has become one of the most valuable assets for organizations. Businesses collect and store massive amounts of information ranging from customer details and financial records to proprietary business intelligence. However, as data volumes grow, so do the risks associated with cyber threats, data breaches, and unauthorized access. This is why database security has become a critical priority for modern enterprises.

Companies across industries must ensure that their databases are protected against both external cyberattacks and internal vulnerabilities. Strong database security strategies not only safeguard sensitive information but also ensure regulatory compliance, operational continuity, and customer trust. Organizations like SYNEXRA TECHNOLOGY SOLUTIONS CO., LTD. recognize that protecting data infrastructure is a fundamental element of sustainable digital transformation.
This article explores why database security is essential for today’s businesses, the risks of inadequate protection, key security practices, technologies involved, and how companies can build a robust database security framework.
Understanding Database Security
What Is Database Security?
Database security refers to the collection of technologies, policies, and procedures designed to protect databases from unauthorized access, misuse, or attacks. It involves securing the database management system (DBMS), the data itself, the applications that interact with the database, and the underlying infrastructure.
The goal of database security is to ensure:
- Confidentiality – Only authorized users can access sensitive data
- Integrity – Data remains accurate and unaltered
- Availability – Systems remain accessible and operational when needed
These three principles form the foundation of modern data protection strategies.
Components of Database Security
Effective database security includes multiple layers of protection, such as:
- Access control and authentication
- Encryption of stored and transmitted data
- Monitoring and auditing of database activities
- Backup and recovery mechanisms
- Vulnerability management
By combining these elements, organizations can significantly reduce the risk of data breaches and system compromises.
The Growing Importance of Database Security
Rising Cybersecurity Threats
Cyberattacks targeting business data have increased dramatically in recent years. Hackers often target databases because they contain valuable information such as:
- Customer identities
- Payment information
- Intellectual property
- Business strategies
Attack methods such as SQL injection, malware attacks, ransomware, and insider threats make database protection more important than ever.
Without proper database security measures, even a single vulnerability can lead to a large-scale data breach.
Increasing Data Volumes
Modern organizations generate and store enormous volumes of data from:
- Customer interactions
- E-commerce platforms
- Mobile applications
- Cloud services
- IoT devices
As data environments grow more complex, managing and securing these databases becomes increasingly challenging.
Database security helps ensure that growing data ecosystems remain protected against potential threats.
Strict Regulatory Requirements
Many industries are subject to strict data protection regulations. Governments and regulatory bodies require organizations to implement strong security controls to protect personal and financial data.
Failure to comply with these regulations can result in severe penalties, legal consequences, and reputational damage.
Strong database security helps organizations maintain compliance with regulations such as data privacy laws and financial security standards.
Key Risks of Poor Database Security
Data Breaches
Data breaches occur when unauthorized individuals gain access to sensitive information stored in databases. These breaches can expose personal information, trade secrets, and financial records.
The consequences of data breaches often include:
- Financial losses
- Legal liabilities
- Reputational damage
- Loss of customer trust
Many high-profile cybersecurity incidents have been caused by weak database security practices.
Insider Threats
Not all database security threats come from external attackers. Employees, contractors, or partners with internal access may intentionally or unintentionally compromise sensitive data.
Insider threats may include:
- Unauthorized data access
- Data theft
- Accidental data leaks
- Privilege abuse
Implementing strict access controls and monitoring systems can help mitigate these risks.
SQL Injection Attacks
SQL injection is one of the most common database attack techniques. Attackers insert malicious SQL code into application inputs to manipulate database queries.
This type of attack can allow hackers to:
- Access confidential data
- Modify database records
- Delete critical information
- Gain administrative privileges

Proper input validation and secure coding practices are essential to prevent SQL injection vulnerabilities.
Data Loss and Corruption
Database failures, cyberattacks, or system errors can lead to data loss or corruption. Without proper backup and recovery systems, businesses may lose critical information permanently.
Reliable database security strategies include regular backups and disaster recovery planning to ensure business continuity.
Core Principles of Database Security
Strong Access Control
Access control ensures that only authorized individuals can access specific data or perform certain operations within a database.
Common access control mechanisms include:
- Role-based access control (RBAC)
- Multi-factor authentication (MFA)
- Least privilege principle
- Identity and access management systems
Limiting user permissions reduces the risk of unauthorized data exposure.
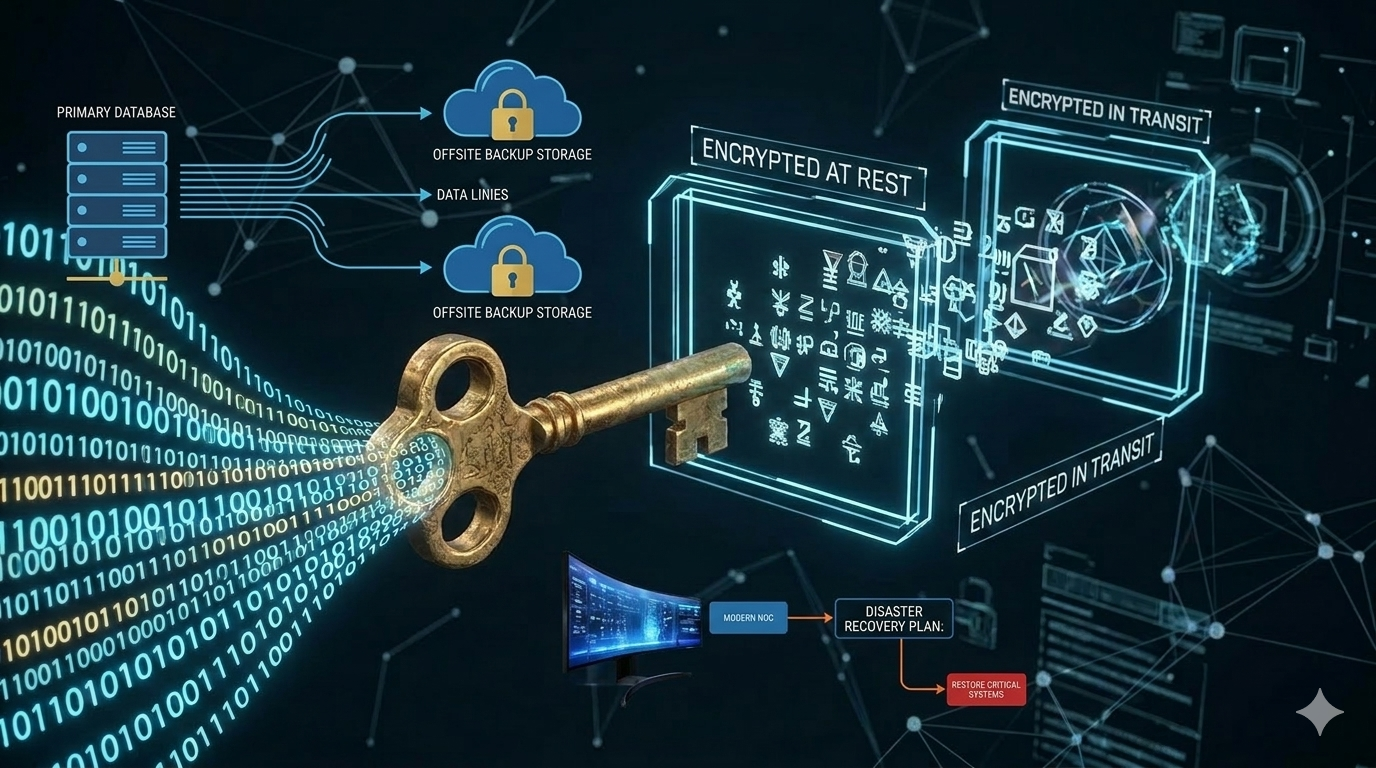
Data Encryption
Encryption is a key component of database security. It protects sensitive information by converting it into unreadable formats that can only be decrypted with authorized keys.
There are two main types of encryption used in database environments:
- Encryption at rest – protects stored data
- Encryption in transit – protects data while being transferred between systems
Encryption ensures that even if attackers gain access to database files, the data remains unreadable.

Database Monitoring and Auditing
Continuous monitoring allows organizations to detect suspicious activities within database environments.
Monitoring systems can track:
- Login attempts
- Query patterns
- Data access events
- Privilege changes
Audit logs provide visibility into database activities and help security teams investigate potential security incidents.
Regular Security Updates
Database management systems and related software must be regularly updated to address vulnerabilities and security flaws.
Outdated systems often contain known vulnerabilities that attackers can exploit.
Routine patch management and vulnerability scanning help maintain a secure database environment.
Best Practices for Database Security
Implement the Principle of Least Privilege
Users should only have access to the data and systems necessary to perform their tasks. Limiting privileges reduces the risk of accidental or malicious data exposure.
Administrators should regularly review and update user permissions.
Secure Database Configurations
Default database configurations may not provide adequate security. Organizations should:
- Disable unnecessary services
- Remove default accounts
- Enforce strong password policies
- Configure firewall rules
Proper configuration management strengthens overall database security.
Conduct Regular Security Assessments
Security assessments help organizations identify vulnerabilities before attackers do.
These assessments may include:
- Penetration testing
- Vulnerability scanning
- Risk assessments
- Security audits
Regular testing ensures that security measures remain effective against evolving threats.
Maintain Backup and Disaster Recovery Plans
Reliable backups are essential for protecting against data loss caused by cyberattacks, hardware failures, or natural disasters, which is why every organization should implement a disaster recovery plan for business continuity.
Best practices include:
- Automated backup schedules
- Secure backup storage
- Offsite backup locations
- Disaster recovery testing
A strong recovery plan ensures that critical systems can be restored quickly.
The Role of Modern Technologies in Database Security
Artificial Intelligence and Threat Detection
Artificial intelligence is increasingly used to enhance database security. AI-powered tools can analyze database activities and detect unusual patterns that may indicate cyber threats.
These systems can automatically alert security teams or trigger protective actions.
Cloud Database Security
As organizations migrate to cloud-based infrastructures, securing cloud databases becomes essential by implementing cloud security practices for modern businesses.
Cloud database security includes:
- Identity and access management
- Encryption services
- Network security controls
- Continuous monitoring
Cloud providers offer built-in security features, but organizations must still configure and manage these systems effectively.
Data Masking and Tokenization
Data masking replaces sensitive information with fictional or anonymized values, allowing organizations to use data for testing or analytics without exposing real information.
Tokenization replaces sensitive data with random tokens that cannot be reversed without a secure token vault.
These techniques reduce the risk of data exposure during development or data sharing.
Building a Strong Database Security Strategy
Establish Security Policies
Organizations should create clear database security policies outlining how data should be stored, accessed, and protected.
These policies should define:
- User access guidelines
- Data classification levels
- Security monitoring procedures
- Incident response protocols
Well-defined policies help ensure consistent security practices across the organization.
Train Employees on Security Awareness
Human error is a common cause of data breaches. Training employees on cybersecurity best practices can significantly reduce security risks.
Training programs should cover:
- Phishing awareness
- Secure password practices
- Data handling procedures
- Incident reporting protocols
Educated employees become an important line of defense against cyber threats.
Integrate Security into Development
Database security should be integrated into the entire software development lifecycle.
Developers should follow secure coding practices and test applications for vulnerabilities before deployment.
This proactive approach reduces security risks in production environments.
The Future of Database Security
As digital transformation accelerates, database environments will continue to evolve. Emerging technologies such as artificial intelligence, automation, and zero-trust architectures will shape the future of database security.
Key trends include:
- Automated threat detection
- Self-healing database systems
- AI-driven anomaly detection
- Zero-trust data access models
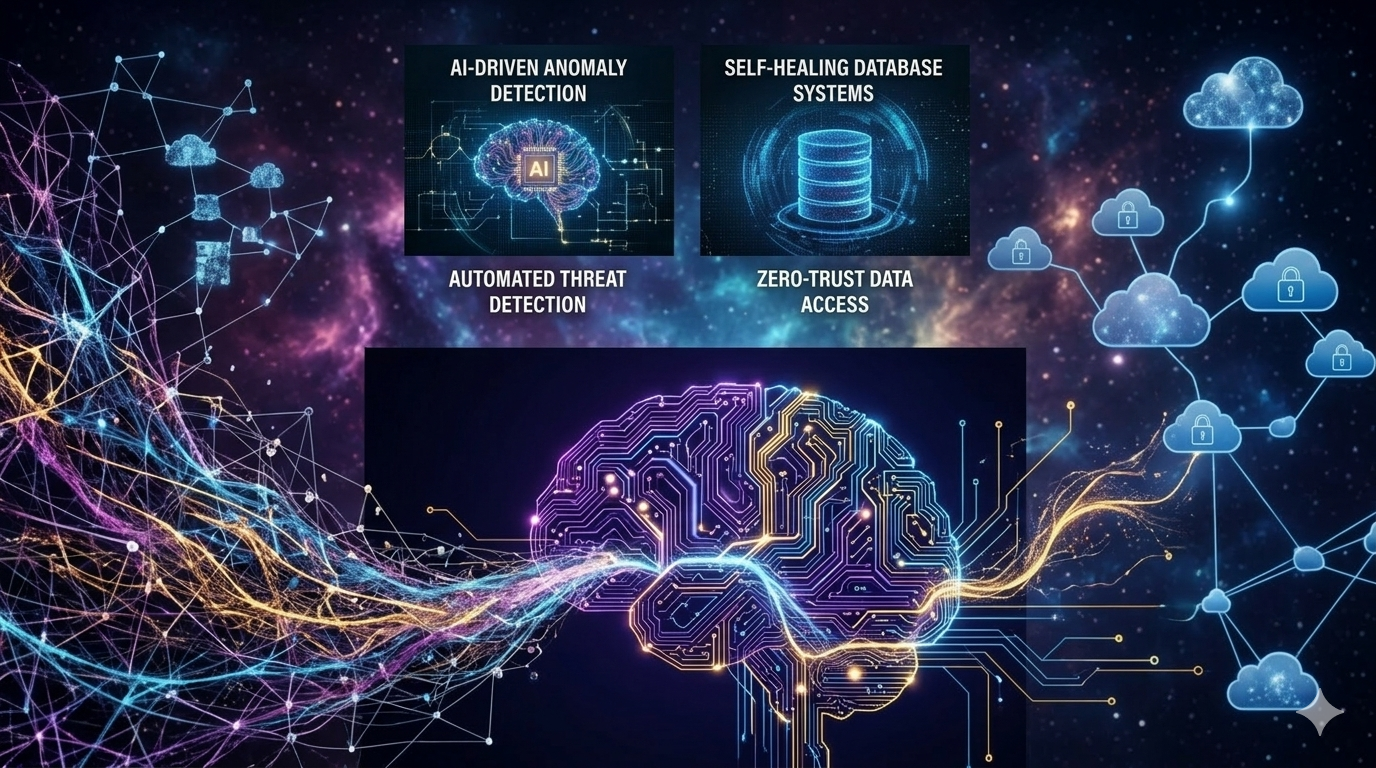
Organizations that adopt advanced security frameworks will be better equipped to protect their data assets in the future.
Conclusion
In an era where data drives business decisions, innovation, and customer experiences, protecting databases is no longer optional. Strong database security safeguards sensitive information, prevents costly data breaches, and ensures regulatory compliance.
Modern organizations must implement comprehensive database security strategies that include access control, encryption, monitoring, and continuous risk assessment. By adopting best practices and leveraging advanced technologies, businesses can protect their critical data assets and maintain operational resilience.
Companies like SYNEXRA TECHNOLOGY SOLUTIONS CO., LTD. understand that effective database security is a cornerstone of modern IT infrastructure. With the right strategies and technologies in place, businesses can build secure, scalable, and trustworthy data environments that support long-term growth and digital transformation.